Spammers and phishers can use the Sender Policy Framework (SPF), DomainKeys Identified Email (DKIM), and Domain-based Message Authentication, Reporting, and Conformance to spoof your domain in the FROM: addresses of email they send (DMARC).
Let’s start with an explanation of the three email anti-spoofing strategies.Sender Policy Framework (SPF)After roughly six years of discussion and debate, SPF was initially published as an experimental RFP in 2006.
IN TXT “v=spf1 mx a:pluto.example.net include:aspmx.googlemail.com -all”According to the DNS zone record above, MX (mail exchanges) that send an email for email addresses from the example.net domain are called pluto.example.net or aspmx.googlemail.com, with all other servers names not authorized.
The keys can be produced in a number of methods, such as using free public sites.
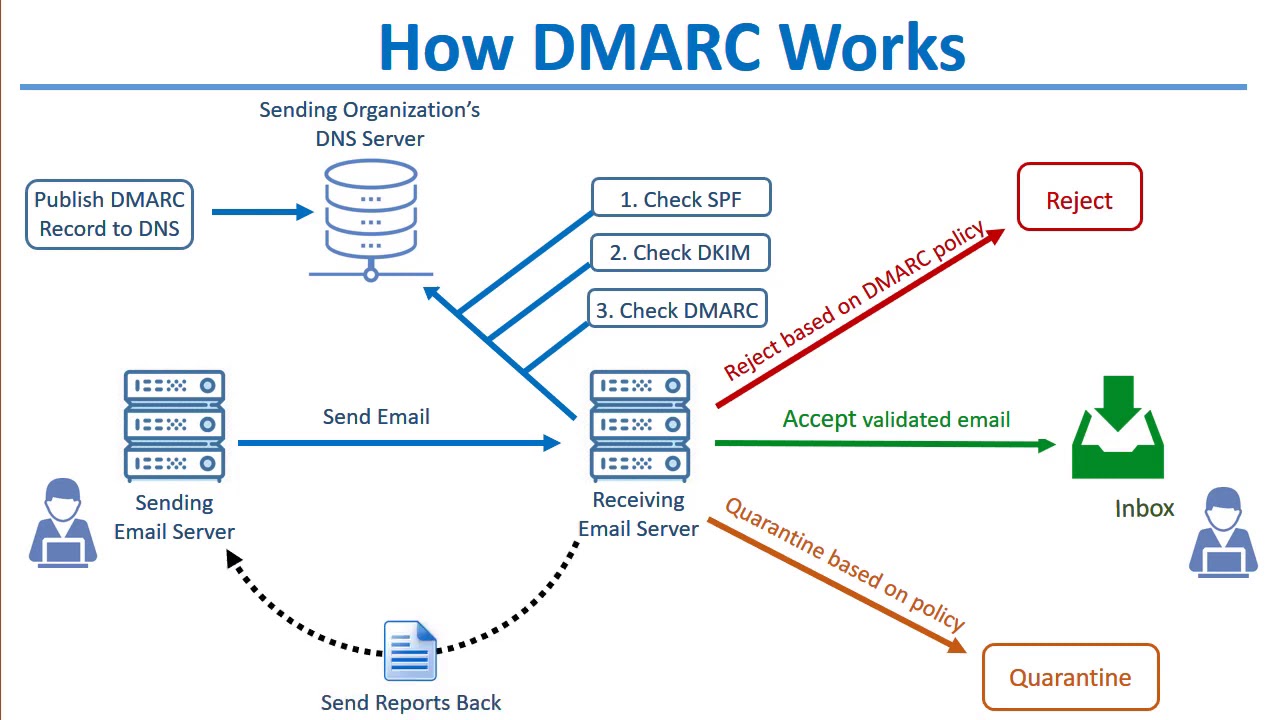
If a message fails the spoofing check, DMARC contains instructions on what actions receiving gateways should take.
It’s established in DNS as a TXT record, just like the others._dmarc.example.net IN TXT “v=DMARC1;p=none;sp=quarantine;pct=100;rua=mailto:dmarcreports@example.net”It states that the version is DMARC1, that there is no policy (both SPF and DKIM should be checked), that the recommended action is to quarantine (or send to spam folders), that almost all emails from example.net should be analyzed, and that reports should be sent to dmarcreports@example.net.And here’s the thing: only 7% of DMARC customers have it configured for “quarantine” or “reject.” They only use it for reporting, negating its effectiveness as an anti-spoofing mechanism.