


The term “vulnerability assessment and penetration testing” (VAPT) covers a wide range of security assessment services with the goal of identifying and reducing cyber security vulnerabilities across the IT infrastructure of a company.
Step 1. Collecting information
During this stage, pen testers acquire as much information as they can on the target’s IT infrastructure, including any resources, systems, applications, networks, etc. As the pentester spends the most time here, it is the most important part of a security test because the more information they learn about the target, the better their chances are of getting useful results when an attack is conducted.
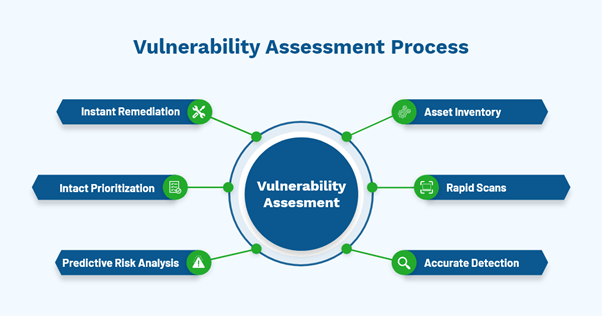
Step 2. Vulnerability Assessment
In this second step, a pen tester used a collection of tools to scan the target application for vulnerabilities and understood how the target would react to various intrusion assaults in both the static and running conditions of the code. This audit offers basic information and identifies any security flaws or dangers that could let a hacker into the environment.
Step 3. Penetration Testing (Extorting vulnerabilities)
In this step, pen testers attempt to access the target in a secure setting by exploiting the vulnerabilities in order to determine the degree to which an attacker can infiltrate a weak system. The tester tries to increase network privileges after any vulnerability has been exposed by intercepting traffic and mapping the internal network to acquire the most access to the system, including sensitive data on apps and file servers.
Step 4. Generate Reports
After the penetration testing is finished, the proof of exploited vulnerabilities must be gathered for assessment and action. The scope of the assessment, testing procedures, a summary of the findings with risk severity, specifics on each finding with their implications, and remedial suggestions are also included.
What is VAPT consist of?
Network penetration testing:
· Identifying weaknesses at the network and system levels;
· Identifying wrong configurations and settings;
· Determining the wireless network’s vulnerability;
· Identifying phony services and weak protocols.
Application penetration testing:
· Identifying flaws at the application level
· Phony requests
· Use of malicious scripts,
· Session management violations.
Mobile app penetration testing:
· This testing reveals weaknesses in the cyber security posture of a mobile application.
· The apps that are evaluated the most frequently are those for iOS and Android.
· Penetration testing for mobile apps helps to safeguard them and lowers the possibility of fraud, malware or virus infections, data leaks, and other security flaws.
API Penetration Testing:
· The cloud, IoT, mobile apps, and web apps have all entered a new era of digital transformation thanks to APIs.
· APIs serve as the underlying framework that enables data to move between systems both inside and outside.
· If deployed APIs are reviewed at all for security, they are not thoroughly tested.
· Either a protected SOAP or REST API.
· The security of the apps for which the API provides services is just as important.
Need a Vulnerability Assessment and Penetration Testing?
VAPT testing could prove to be a very beneficial tool for companies. To shield them from hacker attacks and criminal activity, the security level is increased. Because of this, the majority of firms take it very seriously in order to reap meaningful security benefits.
By safeguarding their connected device networks spanning device-connectivity-application layers utilizing strategic, transformative, and managed operations approaches, Being the Best Vulnerability Assessment and Penetration Testing Company in Jaipur, Elanus Technologies assists businesses in the development, deployment, and management of security products on a worldwide scale.
We have comprehensive knowledge of cyber security, including threat modelling and VAPT across devices. We have the appropriate certifications. More importantly, our staff is made up of seasoned experts that are skilled at identifying security vulnerabilities and providing assistance to fix them. In other words, we rank highly among the market’s security consultants. Our expertise can aid in locating information about your company on the dark web.
Read our Blog:
https://blogs.elanustechnologies.com/vulnerability-assessment-penetration-testing-vapt/


















