


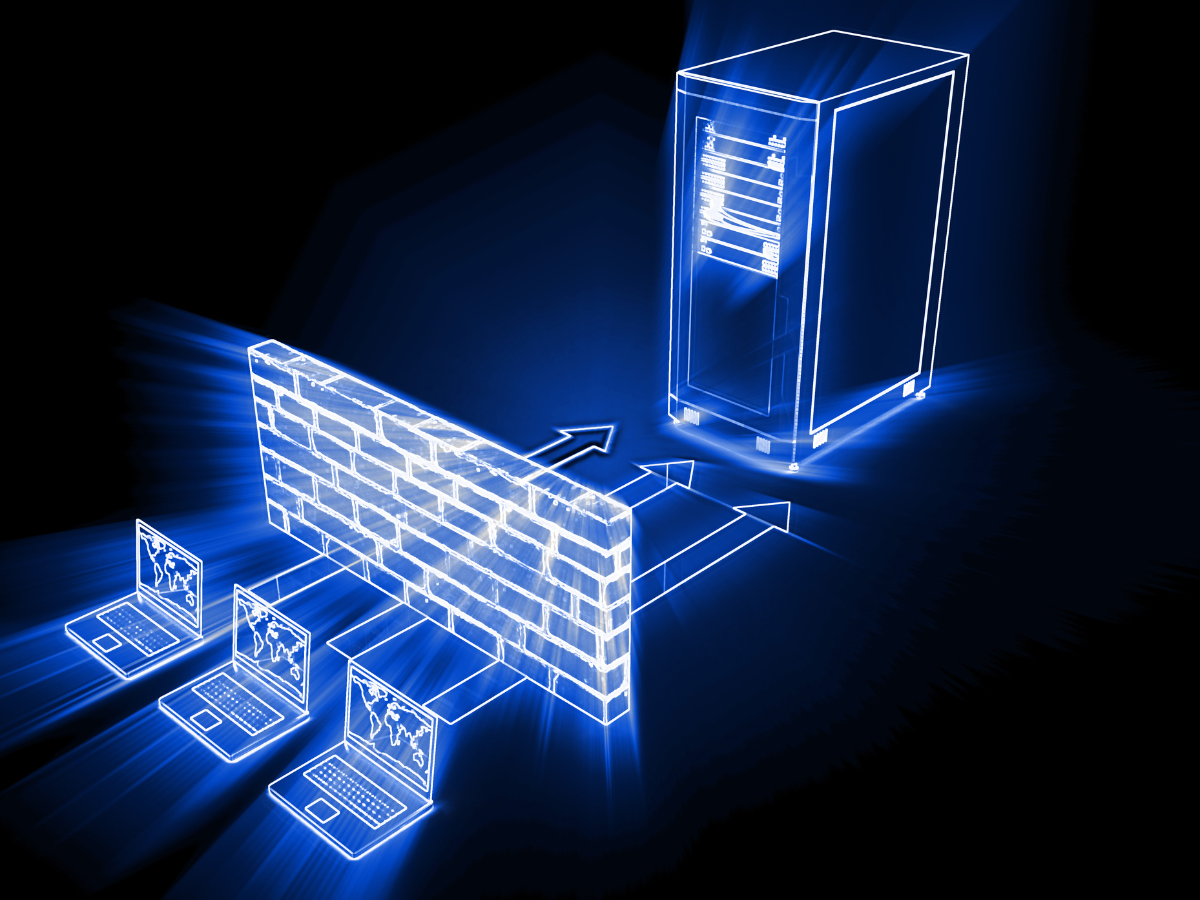
Managing firewall rules effectively is essential for maintaining a secure and efficient network. Misconfigured or outdated rules can create vulnerabilities, allow unauthorized access, and degrade network performance. Using a Firewall Analyzer enables organizations to monitor, evaluate, and optimize firewall rules systematically. Companies like Opinnate demonstrate how advanced tools can transform firewall management, providing visibility into complex rule sets and enabling administrators to maintain secure, compliant, and optimized networks with ease.
Understanding Firewall Rule Optimization
Firewall rule optimization involves reviewing and refining firewall policies to remove redundancy, resolve conflicts, and improve overall network security. Over time, rules can accumulate unnecessarily, often due to legacy configurations or temporary changes that were never cleaned up. Without optimization, these redundant rules can slow network performance, create potential security gaps, and complicate policy management. A Firewall Analyzer helps identify these issues by analyzing rule sets, traffic patterns, and policy effectiveness, providing actionable insights for optimization.
Assessing Existing Firewall Rules
The first step in optimizing firewall rules is a thorough assessment of existing configurations. Advanced Firewall Analyzer tools allow administrators to examine rule usage, detect inactive or rarely used rules, and identify rules that overlap or conflict with others. This analysis is critical for understanding which rules are essential and which ones may be posing unnecessary risks. By establishing a baseline of current firewall rules, organizations can plan a targeted optimization strategy that addresses both security and operational efficiency.
Identifying Redundant and Conflicting Rules
Redundant and conflicting rules are common in networks with complex or multi-vendor firewall environments. Redundant rules perform the same function as others and can cause unnecessary processing overhead, while conflicting rules may inadvertently allow or block traffic incorrectly. A Firewall Analyzer highlights these issues by analyzing rule interactions and traffic patterns. This step ensures that administrators can systematically remove redundant rules, resolve conflicts, and streamline policies for better security and performance.
Prioritizing Rules for Optimization
Not all firewall rules have equal importance. Some rules protect critical assets or regulate high-volume traffic, while others may have minimal impact. Optimizing firewall rules requires prioritization based on risk, relevance, and usage. Firewall Analyzer tools help identify which rules are most crucial and which can be modified, consolidated, or removed. By focusing on high-priority rules first, organizations can reduce risk exposure while gradually improving overall firewall performance.
Implementing Changes Safely
Once redundant or conflicting rules are identified, the next step is implementing changes without disrupting network operations. A Firewall Analyzer often includes simulation and impact analysis features that allow administrators to test rule changes before deployment. This reduces the risk of accidental network outages or unintended security gaps. Implementing changes safely ensures that firewall rules remain effective and that optimization does not compromise the organization’s security posture.
Continuous Monitoring and Adjustment
Firewall optimization is not a one-time task; networks evolve, new applications are deployed, and traffic patterns change. Continuous monitoring is essential to ensure that firewall rules remain effective over time. A Firewall Analyzer provides ongoing visibility into rule usage, alerts administrators to anomalies, and supports continuous improvement. By regularly reviewing and adjusting rules based on real-time data, organizations can maintain optimal security and performance consistently.
Benefits of Using Advanced Firewall Analyzer Tools
Using a Firewall Analyzer offers several benefits for network security management. It provides a centralized view of firewall rules across multiple devices and vendors, automates analysis of complex rule sets, and reduces manual effort. Advanced tools also help maintain compliance by tracking rule changes and generating reports for audits. Organizations like Opinnate leverage these capabilities to simplify firewall management, minimize risks, and ensure that security policies are enforced consistently across the network.
Enhancing Security and Compliance
Optimized firewall rules strengthen overall network security by eliminating vulnerabilities and ensuring that only authorized traffic is allowed. They also support regulatory compliance by maintaining clear and consistent policy enforcement. A Firewall Analyzer ensures that organizations can demonstrate proper firewall management practices to auditors, regulatory bodies, and internal stakeholders. This combination of enhanced security and compliance makes firewall optimization a strategic priority for modern enterprises.
Conclusion
Optimizing firewall rules is essential for secure, efficient, and compliant network operations. Using a Firewall Analyzer simplifies this process by providing visibility, analysis, and actionable insights that enable organizations to streamline policies, remove redundant rules, and resolve conflicts. Companies like Opinnate show that advanced tools not only improve firewall performance but also enhance overall security posture. By following a systematic, step-by-step approach, organizations can ensure that firewall rules are optimized continuously, reducing risks and maintaining a resilient network infrastructure.



















