


The Rising Importance of Secure Software Development
As digital transformation accelerates across industries, software applications have become deeply embedded in daily operations, customer interactions, and critical decision-making processes. This rapid expansion has also increased the attack surface for cyber threats, making security an essential element rather than an afterthought. Modern development teams are under pressure to release features quickly, but speed without security can lead to vulnerabilities that compromise data, trust, and compliance. This reality has pushed organizations to rethink how security fits into the software development lifecycle and to adopt preventive measures that address risks at their origin.
Understanding Source Code Vulnerabilities Early
Security flaws often originate in the earliest stages of development, hidden within the logic, structure, or dependencies of the code itself. Issues such as insecure input handling, improper authentication flows, or flawed data validation can remain unnoticed until exploited in production. This is where Source Code Security Analysis plays a crucial role. By examining application code before deployment, development teams can identify weaknesses that might otherwise evolve into serious security incidents. Early detection not only reduces the cost of remediation but also minimizes disruption, allowing developers to fix issues while the context of the code is still fresh in their minds.
Integrating Security into the Development Workflow
Traditional approaches treated security as a final checkpoint, often conducted just before release. This model is no longer sufficient in agile and continuous delivery environments. Today, security must be woven into daily development practices. Automated checks during coding, testing, and integration ensure that vulnerabilities are addressed incrementally rather than accumulated over time. When security feedback becomes part of the regular workflow, developers gain a better understanding of secure coding principles and naturally produce more resilient applications.
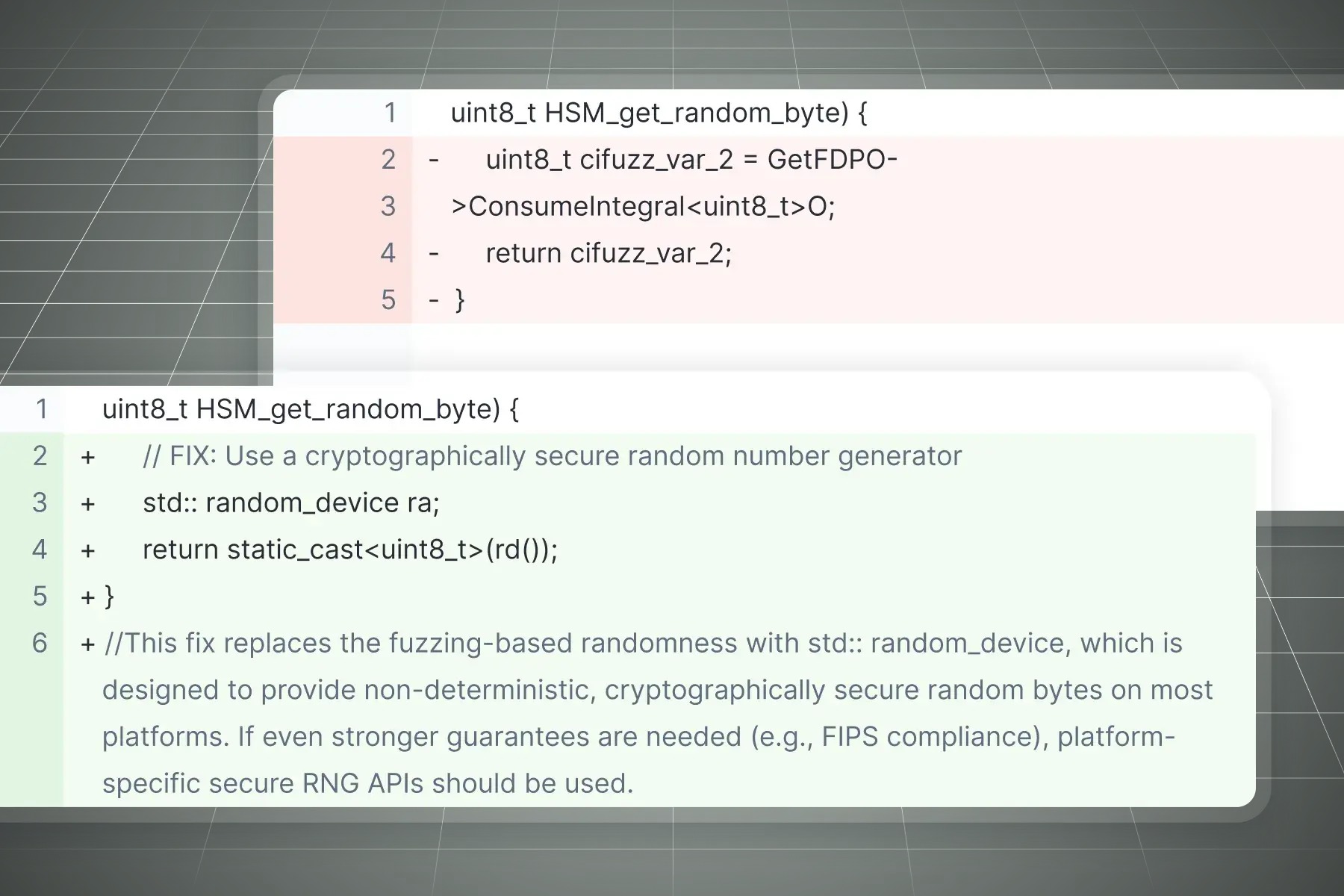
The Role of Automated Static Analysis
Automated static analysis has emerged as a powerful method for identifying vulnerabilities without executing the application. A Sast Security Tool inspects source code, configuration files, and build scripts to uncover patterns associated with known security risks. Because this analysis happens early, often directly within development environments or integration pipelines, it enables teams to address issues before they reach later stages. This proactive approach supports faster releases while maintaining a strong security posture, balancing innovation with responsibility.
Enhancing Developer Awareness and Accountability
One of the often-overlooked benefits of automated security analysis is its educational impact. When developers receive immediate feedback about potential risks in their code, they begin to recognize recurring patterns and understand why certain practices are unsafe. Over time, this fosters a culture of accountability and shared responsibility for security. Rather than relying solely on specialized security teams, organizations empower developers to become the first line of defense against vulnerabilities.
Aligning Security with Business Objectives
Secure software is not just a technical requirement; it is a business enabler. Applications that protect sensitive data and operate reliably build customer confidence and support long-term growth. By identifying and resolving vulnerabilities early, organizations avoid costly breaches, regulatory penalties, and reputational damage. Security-focused development practices also streamline audits and compliance efforts, making it easier to demonstrate due diligence to stakeholders and regulators alike.
Preparing for the Future of Secure Development
As technologies evolve and applications become more complex, the need for robust security practices will only intensify. Cloud-native architectures, microservices, and distributed systems introduce new challenges that demand continuous vigilance. Embedding automated analysis into development pipelines ensures that security scales alongside innovation. By prioritizing early detection, continuous feedback, and developer education, organizations position themselves to meet future threats with confidence.
Conclusion: A Proactive Path to Resilient Software
Building secure software requires a shift in mindset from reactive fixes to proactive prevention. By focusing on code-level analysis, integrating security into everyday development, and leveraging automation, teams can significantly reduce risk without sacrificing speed. The result is software that not only meets functional requirements but also stands strong against evolving threats. In an era where trust and reliability define success, proactive code analysis is no longer optional but fundamental to sustainable digital growth.


















