


Cyber security is very important now in USA, so we must have to know its type. so that we can discuss with the provider of cyber security services in USA .Cybersecurity encompasses various types or categories, each focused on safeguarding different aspects of digital systems and information.
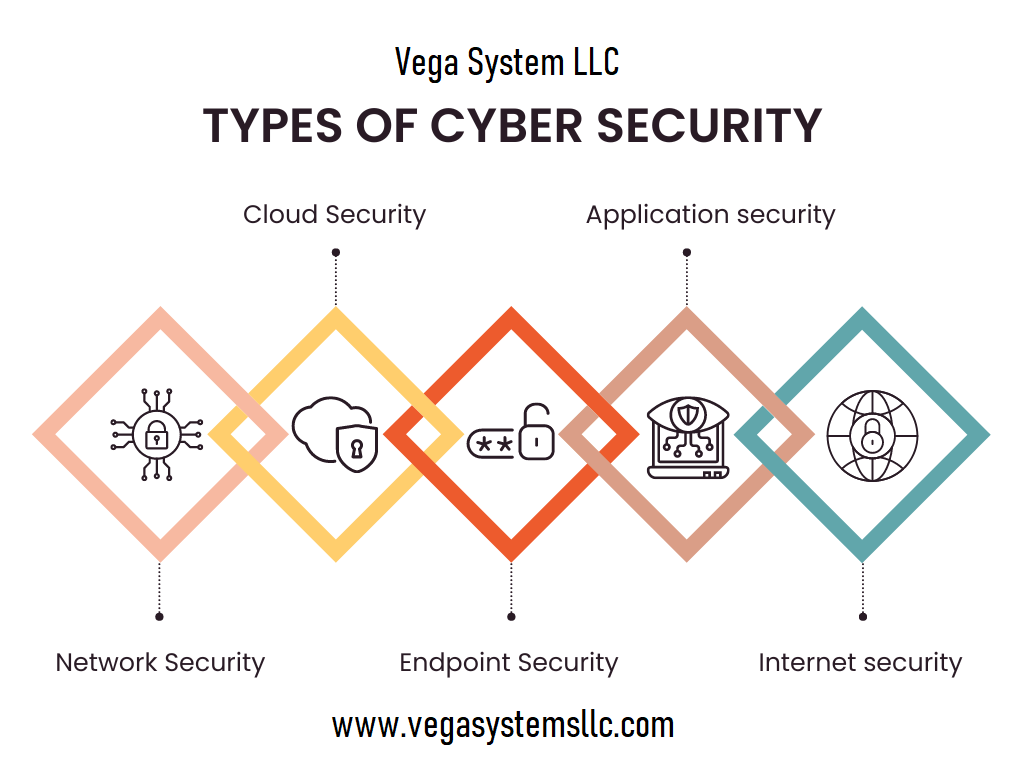
Some common types of cybersecurity include:
Network Security: This type of cybersecurity focuses on protecting the integrity, confidentiality, and availability of data transmitted over networks, including wired and wireless networks. Network security measures may include firewalls, intrusion detection systems (IDS), and virtual private networks (VPNs).
Endpoint Security: Endpoint security involves securing individual devices such as computers, laptops, smartphones, and tablets from cyber threats. Antivirus software, anti-malware programs, and endpoint detection and response (EDR) solutions are commonly used to protect endpoints from various types of attacks.
Cloud Security: With the increasing adoption of cloud computing services, cloud security has become crucial for protecting data stored in cloud environments. Cloud security measures include encryption, access controls, and monitoring to ensure the confidentiality, integrity, and availability of cloud-based resources and data.
Application Security: Application security focuses on securing software applications and preventing vulnerabilities that could be exploited by cyber attackers. Secure coding practices, penetration testing, and application firewalls are used to identify and mitigate security risks in software applications.
Identity and Access Management (IAM): IAM involves managing and controlling user access to digital resources and systems. This includes authentication methods, such as passwords, biometrics, and multi-factor authentication (MFA), as well as authorization controls to ensure that users have appropriate levels of access based on their roles and privileges.
Data Security: Data security involves protecting sensitive information from unauthorized access, disclosure, and manipulation. Encryption, data masking, and data loss prevention (DLP) technologies are commonly used to safeguard data at rest, in transit, and in use.
Incident Response and Management: Incident response and management involve processes and procedures for detecting, responding to, and recovering from cybersecurity incidents such as data breaches, malware infections, and denial-of-service (DoS) attacks. Incident response plans typically include steps for containment, eradication, and recovery to minimize the impact of security incidents.
These are just a few examples of the various types of cybersecurity measures and practices implemented to protect digital assets and information from cyber threats.













.png)




