


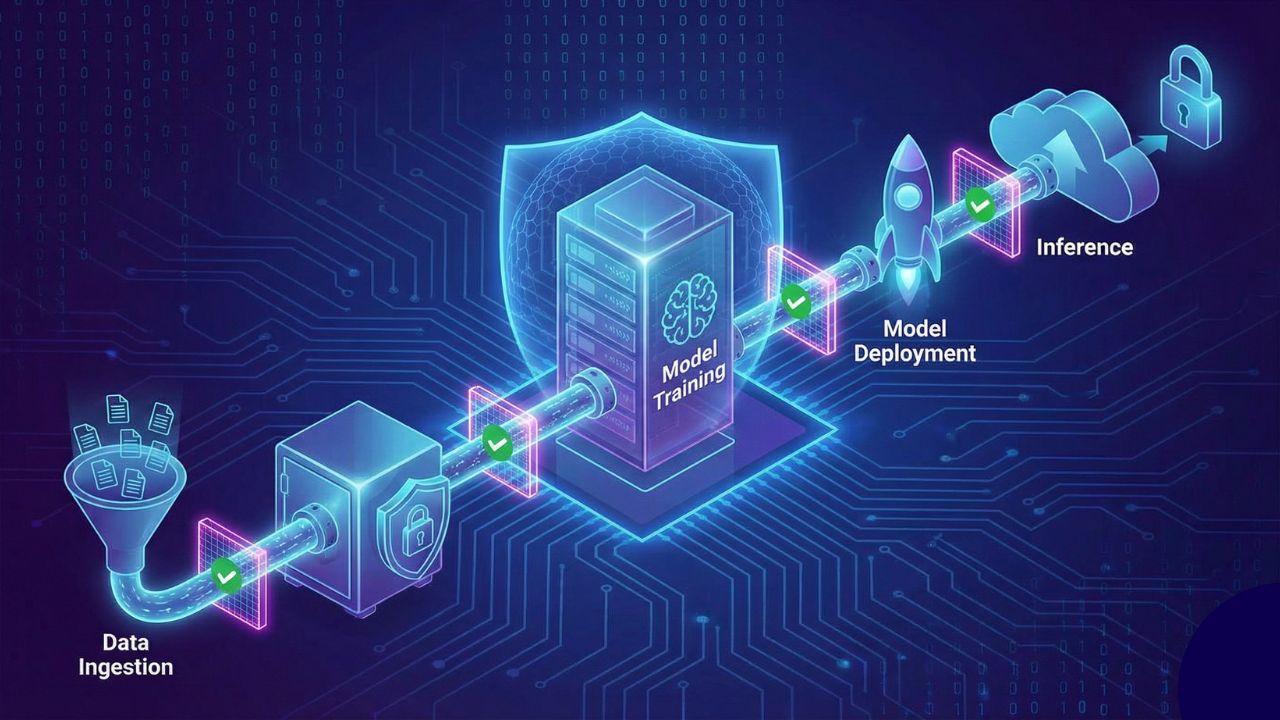
AI pipelines introduce a wide range of security risks as data flows through collection, training, storage, and deployment stages. Each phase creates its own vulnerabilities, and a weakness in any layer can compromise the entire system. Securing AI pipelines from data ingestion to inference requires a clear understanding of how data moves, how models learn, and how attackers exploit gaps across this lifecycle.
Organizations that rely on AI driven decisions must protect their pipelines with the same rigor applied to critical infrastructure. When the data is trusted, the model behaves predictably. When the data or the process is compromised, the entire pipeline becomes unreliable.
Strengthening the Data Ingestion Stage
The pipeline begins with data ingestion, which is often the most vulnerable point. Data comes from multiple sources such as sensors, customer applications, partners, and public datasets. If attackers manipulate these inputs, the model may learn incorrect patterns or reveal sensitive information through inference.
Key protection strategies include
- Verifying the origin and integrity of incoming data
- Filtering out corrupt or malformed data
- Using secure APIs and encrypted channels
- Monitoring for unusual ingestion patterns
By securing ingestion, organizations prevent poisoned or tampered data from entering the pipeline.
Protecting Data During Preparation and Storage
After ingestion, data goes through cleaning, labeling, and transformation. This stage includes heavy human involvement and multiple tools, which increases the risk of leaks and unauthorized access.
- To secure this step, teams should
- Implement role based access control
- Mask or anonymize sensitive attributes
- Apply strict logging to track who touches the data
- Store datasets in encrypted environments
- Validate that transformation scripts have not been altered
Strong controls ensure that attackers cannot modify the data without being detected.
Securing Model Training
Training is a high value target because it shapes the model’s behavior. If attackers poison training sets or interfere with the training environment, the model may develop hidden vulnerabilities or respond incorrectly to specific triggers.
- Training environments should include
- Isolated compute resources
- Verification of dataset integrity before each training cycle
- Continuous monitoring of training trends to detect unusual patterns
- Protection of model checkpoints and version history
A secure training process ensures the model learns from trustworthy data.
Protecting the Model Throughout Deployment
Once the model is trained, deployment brings new challenges. The model becomes accessible through APIs or integrated into applications, creating opportunities for malicious prompts, extraction attacks, or unauthorized interactions.
- To secure deployment, teams must use
- Authentication and rate limits for model endpoints
- Input validation and output monitoring
- Encryption for model artifacts
- Restrictions on how the model interacts with downstream systems
Without these controls, attackers can influence or extract the model’s logic.
Monitoring and Securing Inference
Inference is where the model interacts with real users. Even if earlier stages are secure, inference can still create risk through harmful inputs, unintended outputs, or model drift caused by changing conditions.
- Effective inference security requires
- Real time monitoring for unusual usage patterns
- Detection of prompt injection attempts
- Drift detection to track changes in model behavior
- Alerts for decisions that fall outside approved ranges
Inference security ensures the system remains reliable after deployment.
Conclusion
Securing AI pipelines from data ingestion to inference requires a layered strategy that protects data, processes, and models at every stage. When organizations focus on integrity, access control, monitoring, and verification, they create AI systems that are resilient against manipulation and capable of supporting safe, trustworthy operations. Check out Modern Security's AI Security Certification course for more details.

















